IT Risk Management
Simplify compliance with IT risk management software that supports multiple frameworks. Uncover IT vulnerabilities so you mitigate risks before they turn into costly incidents.

Greater efficiency. Stronger oversight. Less risk.
Unify Risk Data
View all your IT risk data in one central cloud-based software platform. With a high-level perspective based on accurate, relevant, and high-quality data, you can limit audit fatigue and allocate resources effectively. Transform data into strategic decisions that accelerate business goals.

Access Content Subscriptions
Get one-click access to predefined content libraries and ongoing updates for SOC 2, ISO 27001, and 11 additional frameworks in our IT Risk Management solution.

Streamline Compliance Management
Reduce the time and effort it takes to maintain compliance. Use the portal to easily design, plan, test, and report on operational effectiveness.

Automate Workflow Management
Gathering evidence shouldn’t take weeks. Easily collect evidence and documentation with a risk and control owner portal that makes communication and collaboration seamless. Automated notifications and reminders ensure you meet deadlines.

Stop Duplicating Efforts
Eliminate duplicate tests. Our IT Risk Management software automatically uncovers shared controls and applies them to all relevant frameworks, allowing you to achieve multiple certifications quickly and efficiently.

Visualize IT Risk
Gathering evidence shouldn’t take weeks. Easily collect evidence and documentation with a risk and control owner portal that makes communication and collaboration seamless. Automated notifications and reminders ensure you meet deadlines.

Stay in Control and Confidently Give The Green Light.
Request DemoCompliance Frameworks We Support

SOC 2

NIST 800-53

GDPR

GLBA

SOX

ISO 27002
Whatever your needs, Resolver has a solution.
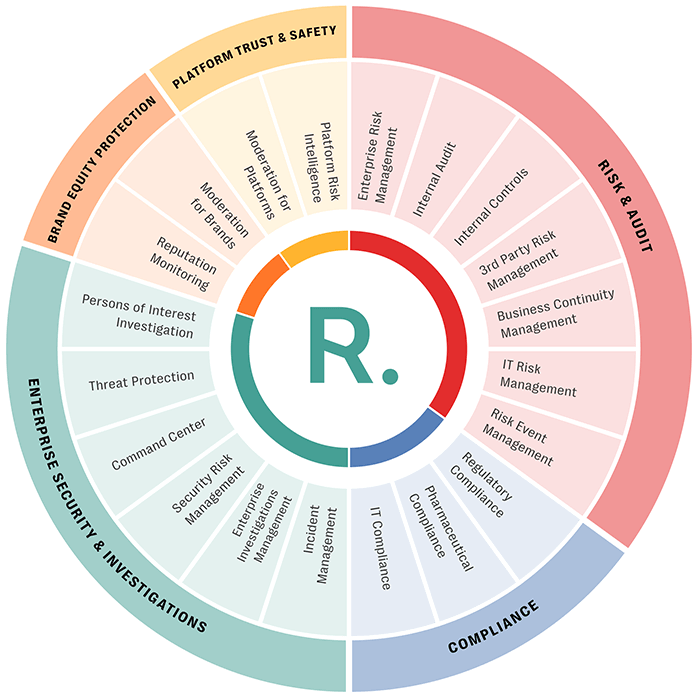
Discover More Products
Enterprise Risk Management Software
Provide your organization’s board and senior leaders a top-down, strategic perspective of risks on the horizon. Manage risk holistically and proactively to increase the likelihood your business will achieve its core objectives.
Regulatory Compliance Software
Save time by monitoring all regulatory compliance activities, providing insights into key risk areas, and then focusing resources on addressing regulatory concerns.
IT Compliance Software
Gain end-to-end IT compliance against multiple frameworks with minimum effort through Resolver’s no-code software solution.