IT compliance frameworks are meant to guide organizations on best practices for managing security risks and protecting sensitive data. It’s important for your company to align with compliance frameworks for both internal and external auditing purposes, stakeholders, new and existing customers, and current staff.
What are common IT regulatory compliance frameworks, and how does Resolver support them?
The Resolver Core platform supports a growing library of content sources to meet the increasing demands of regulators and auditors, and support IT Compliance Management teams. The content packs cover a wide breadth of frameworks to establish best-in-class security practices across multiple industries. Here are the most common IT compliance frameworks that Resolver supports:

SOC 2
SOC 2, or Service Organization Control 2, is a widely recognized auditing standard framework intended for service organizations to report information and assurance about controls relevant to the security, availability, and integrity of IT systems that process user data and information related to user confidentiality and privacy. SOC 2 defines criteria for managing customer data based on five “trust service principles” and produces reports unique to each organization.
Read more: SOC 2 Basics | SOC 2 Checklist
International Organization for Standardization (ISO) Frameworks
ISO/IEC 27001*
ISO/IEC 27001 (2022) provides organizations with requirements for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS). The standard was developed by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) and specifies the requirements for establishing, implementing, maintaining, and continuously improving an ISMS.
Implementation can be done by organizations of all types and involve internal and external parties. The requirements of this standard are generic and are intended to be tailored to the organization’s needs.
Read more on ISO 27001 in our Quick Start Guide.
ISO/IEC 27017*
ISO/IEC 27017 (2015) provides guidelines for information security controls and implementation guidance applicable to the provision and use of cloud services for both providers and customers. This framework includes additional controls specifically related to cloud services and implementation guidance for relevant controls specified in ISO/IEC 27002.
ISO 27799*
ISO 27799 (2016) is intended to be used in accordance with ISO 27002 to help healthcare organizations manage health information security by providing health information security best practice guidelines. By implementing these guidelines, healthcare organizations can ensure the personal health information is at a minimum level of security that is appropriate for their organization.
ISO/IEC 20000-1*
ISO/IEC 20000-1 (2018) provides specific requirements
for establishing, maintaining, and continually improving a service management system, including guidance on the application of service management systems and examples of how to meet the requirements.
ISO/IEC 27002*
ISO/IEC 27002 (2022) is an information security standard published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). ISO/IEC 27002 provides guidelines and general principles for initiating, implementing, maintaining, and improving information security frameworks in an organization.
ISO/IEC 27002 is intended to be used in conjunction with other standards, such as ISO/IEC 27001, to provide a comprehensive framework for information security management in an organization. The standard is applicable to organizations of all sizes and types, across all industry sectors.
ISO 9001*
ISO 9001 (2015) promotes the adoption of a process approach when developing, implementing and improving the effectiveness of a quality management system in order to enhance customer satisfaction by meeting customer requirements.
ISO 22301
ISO 22301:2019 is an international standard for business continuity, helping organizations prepare for and recover from disruptions, ensuring critical operations continue during emergencies.
*ISO content available in certain regions only
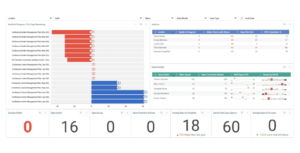
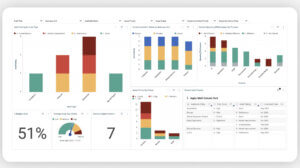
Security Risk Management Report
National Institute of Standards and Technology (NIST) Frameworks
NIST CSF 2.0
The NIST Framework for Improving Critical Infrastructure Cybersecurity, also known as the NIST Cybersecurity Framework (CSF), was published as a voluntary set of guidelines and best practices for managing cybersecurity risk in critical infrastructure organizations. The framework was developed by the National Institute of Standards and Technology (NIST) in response to a 2013 executive order by the President of the United States, which directed NIST to develop a framework that would help organizations manage and reduce cybersecurity risk.
The NIST Cybersecurity Framework is built around five core functions:
- Identify
- Protect
- Detect
- Respond
- Recover
These functions are designed to help organizations manage cybersecurity risk throughout the entire lifecycle of their critical infrastructure assets and systems.
NIST CSF focuses on using business drivers to guide cybersecurity activities and consider cybersecurity risks as part of the organization’s risk management processes. Organizations of all sizes, degrees of cybersecurity risk, or cybersecurity sophistication, can apply the principles and best practices of risk management to improve the security and resilience of critical infrastructure using this framework.
Learn more in our Ultimate Guide to GRC Software
FedRAMP
The Federal Risk and Authorization Management Program (FedRAMP) is a United States federal government-wide program that provides a standardized approach to security assessment, authorization, and continuous monitoring of cloud products and services. The program is designed to ensure that federal agencies can adopt cloud computing technologies quickly, securely, and cost-effectively by providing a standardized and consistent approach to security and risk management.
The FedRAMP program defines a set of security controls and requirements that cloud service providers (CSPs) must meet to receive authorization to provide services to federal agencies. The program also provides a marketplace for federal agencies to search for and select authorized cloud service providers.
Once FedRAMP has authorized a CSP, it’s listed on the FedRAMP Marketplace, where federal agencies can search for authorized cloud service providers and review their authorization documentation. This makes it easier for federal agencies to adopt cloud computing technologies, with the ability to select from a pre-approved list of CSPs that have already been vetted for security and risk management.
The FedRAMP program is managed by the General Services Administration (GSA), in collaboration with NIST and other government agencies.
NIST Privacy Framework
This publication describes the voluntary NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management (Version 1.0). The Privacy Framework is a tool developed to help organizations identify and manage privacy risks to build innovative products and services while protecting the privacy of individuals.
The Privacy Framework provides a flexible, risk- and outcome-based approach, intended to be widely usable by organizations of all sizes and agnostic to any particular technology, sector, law, or jurisdiction. The Privacy Framework follows the structure of the NIST Cybersecurity Framework to facilitate the use of both of these IT compliance frameworks together.
Read Everything You Need to Know in Our Ultimate Guide to Regulatory Compliance Software
NIST 800-53 Rev. 5
The purpose of the NIST 800-53 Rev. 5 publication is to provide a complete approach to information security and risk management by providing organizations with the security controls necessary to fundamentally strengthen their information systems and their operating environments.
The security and privacy controls have been designed to be largely policy/technology-neutral to facilitate flexibility in implementation. This content pack contains the most recent NIST 800-53 Rev. 5 update and supplementary document NIST 800-53 Rev. 5 to address the increasing sophistication of cyberattacks.
NIST 800-53 Rev. 5 is widely recognized as a leading set of security controls for information systems and organizations. It is often used as a basis for other security and IT compliance frameworks and standards, such as FedRAMP and the Cybersecurity Maturity Model Certification (CMMC).
NIST 800-171
NIST 800-171 Rev. 2 (2020) provides agencies with recommended security requirements for protecting the confidentiality of Controlled Unclassified Information (CUI) resident in non-federal systems and organizations. The requirements apply to all components of non-federal systems and organizations that process, store, and/or transmit CUI, or that provide security protection for such components.
Enforcement of these requirements is managed directly by the Department of Defense. NIST 800-171/A is an update to the original NIST 800-171 publication, which was released in 2016. The “A” in the revised version stands for “Assessment,” as it provides additional guidance on how organizations can assess their compliance with the security controls outlined in the publication.
The security controls in NIST 800-171/A are organized into 14 families, including access control, incident response, and system and communications protection. The controls are designed to provide a baseline level of security for protecting CUI and are customizable based on an organization’s specific needs. NIST 800-171/A is not a mandatory compliance framework, but organizations that handle CUI are required to comply with the FAR Clause 52.204-21. Compliance with NIST 800-171/A can help organizations meet these requirements and demonstrate that they have implemented appropriate security controls to protect CUI.
Privacy legislations
GDPR
The General Data Protection Regulation (GDPR) is an EU law that regulates the collection, use, and storage of personal data, ensuring the privacy and rights of individuals. It applies to organizations inside and outside the EU handling EU residents’ data.
PIPEDA
PIPEDA is Canada’s privacy law that governs how organizations collect, use, and disclose personal information in commercial activities, requiring consent and safeguarding data privacy.
CCPA
The California Consumer Privacy Act (CCPA) gives California residents rights over their personal data, allowing them to know, delete, and opt out of the sale of their information. It applies to certain businesses based on revenue or data handling thresholds.
Other common IT compliance frameworks
PCI DSS 4.0
The Payment Card Industry Data Security Standard (PCI DSS) is a global standard that provides a baseline of technical and operational requirements designated to protect payment data. PCI DSS version 4. 0 is the next evolution of the standard. PCI DSS 4.0. Developed with Global Industry Collaboration, PCI DSS 4.0 provides organizations with a more comprehensive and flexible set of security standards to protect against the evolving threats to cardholder data.
CMMC
Designed by the United States Department of Defense (DoD), the Cybersecurity Maturity Model Certification (CMMC) framework consists of maturity processes and cybersecurity best practices from multiple standards, frameworks, and other references, as well as inputs from the Defense Industrial Base and Department of Defense stakeholders.
Assess Your Enterprise Risk Management Maturity in 5 Steps
What are framework content mappings?
Framework enhancements are additional developments that provide depth to our framework offerings and are automatically included with framework subscriptions. These enhancements are unique to Resolver and were included to enhance customers’ compliance efforts and effectiveness.
Organizations often utilize multiple IT compliance frameworks to guide their cybersecurity strategy and certification goals. Quite often, there are significant overlaps in evidence and controls between frameworks.
Framework mappings are leveraged to draw connections between these overlaps and allow customers to easily document their compliance across multiple frameworks rather than creating compliance documentation specific to each one. These mappings show where existing controls may fulfill new framework requirements and allows companies to focus and consolidate their efforts while offering a single source of truth.

Visualization of RCM Compliance Overview Dashboard
IT framework mappings Resolver offers:
- FFIEC: NIST CSF 2.0
- FFIEC: PCI DSS 4.0
- PCI DSS 4.0: NIST CSF 2.0
- PCI DSS 4.0: ISO 27001 (2022)
- SOC 2: ISO 27001 (2022)
- SOC 2: PCI DSS 4.0
- SOC 2: NIST 800-53 rev. 5
- SOC 2: NIST CSF 1.1
- SOC 2: NIST CSF 2.0
- ISO 27001 (2013): ISO 27001 (2022)
- ISO 27001 (2022): NIST CSF 2.0
- NIST 800-53 rev. 5: ISO 27001(2022)
- NIST 800-53 rev. 5: NIST CSF 2.0
- NIST 800-171 rev. 3: NIST 800 171 rev. 2 • NIST 800-171 rev. 2: PCI DSS 4.0
- NIST CSF 1.1: NIST 800-53 rev. 5
- NIST CSF 1.1: ISO 27001(2022)
- NIST CSF 1.1: SOC 2
- NISF CSF 1.1: NIST CSF v2.0
- NIST CSF 2.0 – FFIEC
- NIST CSF 2.0 – NIST 800-53 rev. 5
- NIST CSF 2.0 – PCI DSS 4.0
- NIST CSF 2.0 – SOC 2
- NIST CSF 2.0 – ISO 27001(2022)
Request a demo to see how Resolver can meet your IT compliance regulation and framework requirements, or learn more here.
