Understanding Differences Between Activity, Incident, Investigation, and Case Management in Corporate Security

It’s funny how the lines between incident management vs case management and investigations can blur in the chaos of corporate security. I’ve seen it happen countless times — an incident pops up, everyone scrambles to respond, and before you know it, you’re knee-deep in a tangled mess of data, investigations, and case files. If this sounds familiar, trust me — you’re not alone.
But here’s the thing: understanding the differences between incidents, investigations, and case management is crucial if you want to build a resilient security program. I can’t tell you how many times I’ve had conversations with security teams where these distinctions were the missing puzzle piece in improving efficiency and reducing long-term risk. Activity, incident, investigation, and case management are all related to managing and tracking different types of events or actions within an organization.
In the context of enterprise or corporate security, the definitions of activity, incident, investigation, and case management are similar to their general definitions but with a specific focus on security-related events. The essential difference is the management and reporting of single events (one-to-one) versus the project-level management of multiple incidents — including an incident’s associated activities — and investigations that have been linked together to form a case (one-to-many).
Let’s dive in. I’ll walk you through what sets these three apart and how getting them right can transform the way your team handles corporate security.
What is activity tracking?
Before we go deeper into incidents vs case management and investigations, let’s touch on activity tracking — another key part of corporate security. Activity tracking refers to the process of managing and monitoring routine security-related tasks within your organization. These might include things like:
- Managing access control systems
- Monitoring security cameras
- Conducting regular security audits
- Performing employee training on best practices
Unlike incidents, activities typically involve routine duties that don’t necessarily indicate an immediate threat but are vital in preventing incidents. Tracking activities helps ensure that your security measures are functioning as intended.
That said, activities and incidents aren’t always separate. While activities typically track response times, officer logs, and total time spent, an activity can escalate into an incident if a more serious event unfolds. Proper corporate security incident management ensures that activities and incidents are linked, so you have a complete picture of what led to the incident and can take proactive steps to prevent similar issues in the future.
What is an incident?
In corporate security, incident management refers to the process of managing and resolving security-related incidents within an organization. These incidents can range from physical security breaches, theft or fraud, and workplace violence to other critical security events. The goal of incident management is simple: minimize the impact of the incident and restore normal operations as quickly as possible.
But managing incidents effectively requires more than just a quick fix. It’s about capturing every detail, from the moment the incident occurs through its resolution, to ensure that the right data-driven insights are gathered for improving future responses.
When an incident occurs — whether it’s a theft, assault, or accident — your team’s immediate response is tracked through an activity report. This report is a record of the incident’s key details: the who, what, where, when, why, how, and how much. In essence, it’s the story of a single event.
However, not all incidents end with just that initial response. Some require deeper analysis. This is where incident reporting comes in. Incident reports are more comprehensive, capturing additional details that can be referred to or added to over time, forming a complete picture of the incident.
For example, when you’re managing an incident through Resolver’s platform, we encourage teams to keep the reporting process simple. Why? Because the easier it is to file reports, the more likely incidents will actually get documented — giving you the data you need to make informed decisions over time.
And here’s an important distinction: incident reports are often linked with investigation details, especially if the incident escalates or uncovers systemic vulnerabilities. This helps move beyond just managing the immediate event to truly understanding and addressing the root cause, setting the stage for future prevention.
What is an investigation?
After an incident occurs and the initial dust settles, the next step in corporate security is often an investigation. This is where your team dives into the why — the root cause behind the incident, who was involved, and how to prevent it from happening again.
While incident management is about fast action and recovery, investigation management is about digging deeper. It’s not just about reacting to the immediate event; it’s about solving the puzzle. This process involves collecting extensive data, identifying patterns, and uncovering the vulnerabilities that led to the incident in the first place.
In most organizations, investigations follow a tiered response system. Frontline personnel handle the initial incident response and provide an incident report—a snapshot of what happened. But if the incident is more complex or significant, it’s passed on to the investigations team, where things go into investigation mode. This is where the real detective work begins.
Take, for example, a theft in the workplace. The incident report might detail who was involved, what was stolen, and when it happened. But the investigation will look much further. It will ask: How did the theft occur? Were there any gaps in access control? Was it a one-off event, or part of a pattern?
In the course of an investigation, you’re not just documenting the immediate facts. You’re analyzing every possible factor that contributed to the incident and piecing together a more complete story. This often involves the collection of various investigative data points, including:
- Investigation start and end dates (these often differ from the timeline of the incident itself).
- Assigned investigators and their roles.
- Investigation metrics such as time spent and resources allocated.
- Interviews and summaries from involved parties that go beyond the initial incident report.
- Logs tracking the progress of tasks and expenses.
- Evidence and property records, including the chain of custody, so you know where each piece of evidence is at all times.
In Resolver’s platform, these details are captured under a separate Investigation tab, keeping them distinct from the initial incident report. This separation is important, especially when dealing with sensitive data or ensuring that only the right people have access to critical investigative details.
Here’s something I see often: as multiple incidents occur across an organization, certain patterns or links among incidents start to emerge. Maybe you’re seeing recurring thefts in different locations, or a series of cybersecurity breaches that all seem related. Cross-referencing these incidents is crucial to connecting the dots and spotting systemic issues that may be affecting your security landscape. That’s where case management starts to overlap with investigations, tying multiple incidents together into a larger investigation.
In essence, investigations help you see the bigger picture. They’re your chance to go beyond simply resolving the event and get to the heart of why it happened, so you can prevent future incidents and reduce long-term risk.
What is case management?
Case management refers to the process of managing an ongoing security-related issue within an organization. These can include things like internal fraud investigations, data breaches, or legal disputes related to security incidents. Case management in corporate security involves tracking the status of the case, assigning tasks to individuals, and ensuring that all relevant information is documented and accessible for legal or regulatory purposes. Case management is typically a proactive process, involving ongoing management of a complex issue over time.
Because case management involves overseeing multiple investigations at once, it requires a high degree of project management. Often, a case involves a series of events that are related but not necessarily alike. These events will, nonetheless, be managed and investigated as a single project or case. For example, a case called “Jeff Brown Restraining Order” may be comprised of a series of incidents of varying types, all involving Jeff Brown. All the events are separate incidents with separate investigative details, but they are all managed as a single investigative unit or project.
Depending on the case, a case manager may be assigned to oversee the group of investigators and agencies involved in each of the incidents or the case manager may be tasked with singlehandedly taking over all the investigative work. No matter what responsibilities the case manager is assigned, the case data collected must be continually added to the appropriate records to ensure accurate intelligence is generated. In Resolver, a case is a compilation of multiple investigations, their associated incidents, and those incidents’ linked activities, if any. When adding a new case, you must give it a name and include relevant details, such as the names of case managers and investigators.
Key differences: Incident vs Investigation vs Case Management
| Aspect | Incident | Investigation | Case Management |
| Focus | What happened? | Why did it happen? | How does this connect to other issues? |
| Objective | Quick response & recovery | Root cause analysis | Holistic management of linked issues |
| Data | Event details (who, what, when) | Patterns, connections, and trends | Overarching view of incidents and investigations |
| Outcome | Restoring normal operations | Preventing future incidents | Managing ongoing risks at scale |
Each process plays its role, but they work best when connected. Incidents tell you what happened, investigations explain why it happened, and case management ensures you’re addressing the bigger picture — from minor breaches to long-term risk reduction.
Why understanding these differences matters
Now, here’s why this distinction is so important: if your organization doesn’t differentiate between incidents, investigations, and case management, you’re likely missing critical insights. You might be solving today’s problem, but without understanding the root causes, you’re setting yourself up for tomorrow’s crisis.
Here’s a quick breakdown of why each one matters:
- Incident Management: Helps you respond to threats in real-time, minimizing damage and restoring operations quickly.
- Investigation Management: Identifies the underlying causes of incidents so you can prevent them from happening again.
- Case Management: Provides a holistic view of your security landscape, allowing you to connect incidents and investigations for long-term risk reduction.
If these processes aren’t working together, you’re leaving too much to chance — and in corporate security, chance isn’t something you can afford.
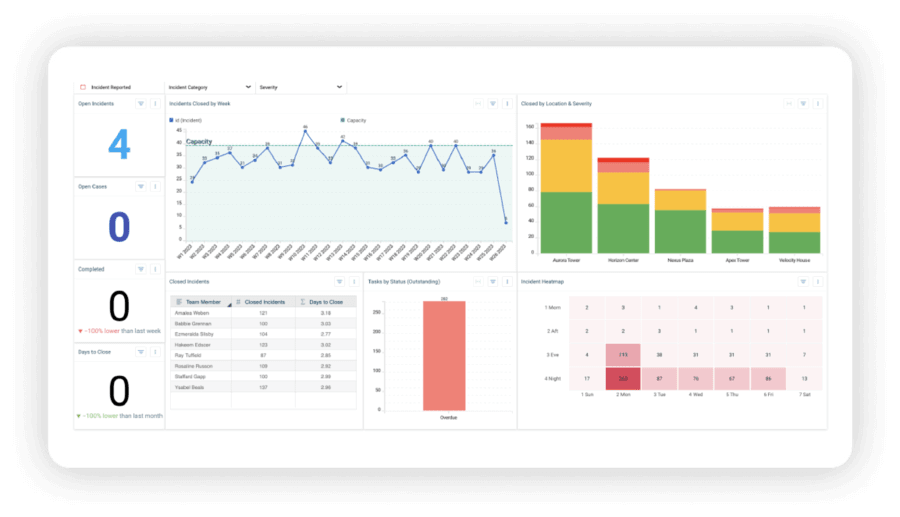
Resolver’s Incident Investigations Dashboard
How Resolver helps you manage your corporate security operations holistically
At Resolver, we’ve designed our platform to make the transition from incident management to investigations and case management seamless. Our tools help you manage every stage of the process, from the first security incident report to the final case outcome.
- AI-powered data tagging helps you sort through massive amounts of data, automatically linking related incidents and identifying patterns that might be missed manually.
- Customizable workflows ensure your team is following best practices for every case type, from brand protection to loss prevention.
- Automated reporting gives you instant insights into the status and outcomes of cases, helping you stay compliant and keep stakeholders informed.
And the best part? It all happens in one platform — no more juggling between disconnected systems or manual data entry. Just faster, smarter investigations that help you get ahead of the risks before they escalate.
It’s time to rethink how you manage security operations
Understanding the differences between incidents, investigations, and case management is the first step to building a more resilient security strategy. When you’re clear about what role each plays, you can respond faster, dig deeper, and reduce risks across your entire organization.
Ready to see how we can help your team manage incidents, investigations, and cases with ease? Let’s chat. Book a personalized tour of Resolver’s Corporate Security Software today and discover how it can transform your security operations across incident management, investigations and case management, and much more.
About the author: As Chief Product Officer at Resolver, Joe Crampton leads product strategy, development, and innovation for our Risk Intelligence Platform and solutions. With over 20 years of experience in enterprise software, Joe is known for his expertise in human-computer interaction, product management, and aligning technology with business needs. He brings a thoughtful, collaborative approach to solving complex risk, compliance, and security challenges through his passion for building tools that help organizations become more resilient.
FAQs: Incident and Investigations Case Management with Resolver
1. What’s the difference between an incident and an investigation?
An incident is an event that disrupts normal operations, while an investigation examines the root cause to understand why the incident occurred and how to prevent it in the future. Incidents could involve security breaches, workplace accidents, or system failures, whereas investigations look deeper into these events to identify causes, responsibilities, and corrective actions.
2. How does case management relate to incidents and investigations?
Case management organizes and oversees multiple incidents and investigations, allowing teams to uncover broader issues and long-term risks. By connecting related incidents and investigations, case management helps identify patterns, root causes, and preventive strategies, ensuring that no risks are overlooked.
3. Can Resolver’s platform help with both incident and case management?
Yes, Resolver’s platform integrates incident management, investigations, and case management into a single system, streamlining workflows and improving efficiency. Our all-in-one platform allows users to handle everything from logging incidents to managing complex investigations and cases, with automation features to enhance reporting and decision-making.
4. How does AI help in investigations?
Resolver’s AI-powered tools automatically tag and link data, enabling teams to uncover connections and patterns faster for deeper insights and quicker resolutions. AI in Resolver’s platform identifies relationships between incidents, flags anomalies, and suggests actionable insights, helping teams focus on critical tasks rather than manually sifting through data.
5. What types of cases can Resolver manage?
Resolver can manage various types of cases, including brand protection, workplace violence, loss prevention, and fraud investigations, with customizable workflows for each. Each case type can be tailored to an organization’s specific needs, ensuring that workflows, reporting, and investigations are aligned with both industry standards and company protocols.