When something goes wrong at work — whether it’s a small hiccup or a major issue —you try to get to the bottom of it as quickly as possible. You get out your magnifying glass, looking for clues and patterns to understand the “why” behind the incident.
But why bother with all this? Simple. It’s about making your workspace smarter, safer, and better. You’re learning from what went wrong to make sure it doesn’t happen again. And it’s not about pointing fingers; it’s a fair, unbiased deep-dive that helps everyone in the long run.
Incident analysis is about learning from mistakes, improving processes, and being prepared so organizations have a safety net that keeps getting stronger every time it’s used.
Top 10 tips & tricks for incident analysis
From laying down the groundwork to wrapping things up with a bow, these tips for incident analysis from our experts aim to make organizations safer, one step at a time — from establishing the basics to leveraging results to assess, manage, and mitigate risk.
Below are the 10 tips they highlighted for effective incident analysis:
1. Answer the basics
Before you can do any sort of analysis, you need to accurately record the relevant information. Document what happened, when it happened, where it happened, why it happened, who was involved, and how much was lost. Then, be consistent with your documentation across the board. With proper policies and procedures in place at the front end, you can go a long way in ensuring accurate and meaningful incident analysis on the back end.
2. Share security information enterprise-wide
The more data you have, the more you’ll be able to cross-reference and compare, and the more meaningful your conclusions will be. There’s tremendous value in going beyond one location, or one department, to get an enterprise-wide understanding of your incident analysis and investigation activity.
Appreciating the sensitivity of this information, the most effective incident management systems allow you to segregate your data at various levels with some users restricted from reviewing (or analyzing) incident activity beyond their locations while others are granted access across the board.
3. Track costs including losses and recoveries
Understanding how much an incident really impacts your organization is like checking your bank statement to see where your money is going. Similarly, tracking costs, including losses and recoveries, gives you a clear picture of the financial impact of what happened.
When you track these costs, you’re piecing together a story of what the incident cost you, not just in terms of money, but also in resources, time, and effort. If you notice certain types of incidents are draining more resources than others, or if your recovery strategies are as effective as you thought, you can make smarter decisions, tweak your processes, and maybe even prevent similar incidents in the future.
Plus, it’s a great way to show the higher-ups the value of investing in safety and incident prevention — because, let’s face it, everyone understands the language of money.
4. Set yourself up to easily perform analyses and quickly generate reports
To make sense of the data you’ve collected and draw meaningful insights, correlating it becomes key. This involves linking different pieces of data, such as location, date, and classification, to understand the bigger picture. The challenge here is that this process can be complex and time-intensive.
Manual data correlation can feel like a daunting, if not impossible, task. This is where automated systems come into play. They can handle this correlation to various extents, saving you from the nitty-gritty of manual work. The right system will reduce or even eliminate the need for manual data manipulation, streamlining your incident analysis process and helping you focus on what really matters – the insights and learnings from the data.
Also read: How to Eliminate Risk Reporting Challenges and Unlock Risk Intelligence
5. Consider the investigative relevance
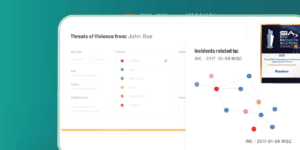
Data mining and investigative queries are crucial tools that empower you to unravel key details such as identifying the people involved, understanding the timeline of events, and uncovering the reasons behind what occurred. It’s a process that requires dedicated time to sift through data for crucial investigative facts.
To get to the heart of an incident, it’s essential to scrutinize your data for any repeating patterns, specific names, or other pertinent details. These elements can be the key to resolving an open case, offering insights that might have been overlooked initially. By meticulously examining this data, you can piece together a clearer, more comprehensive narrative of the events, leading to more informed conclusions and actions.
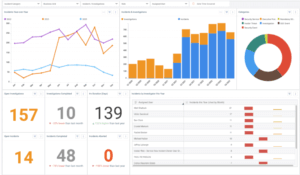
6. Measure current performance against past performance
To gauge the progress or setbacks of your organization, it’s crucial to analyze performance over various time periods. For a comprehensive understanding, you need access to historical data, encompassing a broad range of timelines, not just limited to year-to-year comparisons, but also month-to-month, or even over longer periods.
The key is having the ability to effortlessly retrieve and manipulate data from different time frames. Doing so allows you to track and compare performance, identifying trends, growth, or areas of decline. While numerical data provides the raw insights, the power of visualization through graphs and charts cannot be overstated. They transform complex data sets into easily digestible, visual representations, making it simpler to identify patterns, peaks, and troughs in performance over time, and effectively communicate these insights to diverse audiences.
7. Address operational effectiveness and defend your budget
Resource allocation in any security department is critical and should be based on identified issues and patterns of recurring problems. However, before this can happen, there’s a need to secure the necessary funding. To achieve this, it’s important to compile comprehensive reports, create informative graphs, and gather statistics. These elements collectively showcase the efficiency and value your security team adds to the organization.
Doing so not only highlights past successes but also underscores potential areas for improvement while assessing your incident analysis tools. By presenting a clear picture of how additional investments — be it in technology, operations, or manpower —can further enhance your department’s effectiveness, you create a compelling case for increased funding.
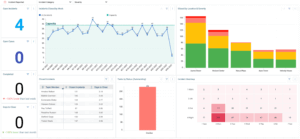
8. Support knowledge-based decisions with statistical evidence
Identifying trends, monitoring losses and threats, disseminating information, executing analytical queries, and creating graphical reports is pivotal in forming decisions rooted in knowledge during the incident analysis process. These actions ensure that the decisions are substantiated by tangible evidence and reliable data, which are more likely to be embraced by management.
Relying on subjective statements like “I think” or “I believe” may have limited impact. In contrast, presenting concrete statistics and factual data provides a compelling and indisputable basis for decision-making, effectively strengthening your argument and enhancing its credibility.
9. Focus on pattern analysis and trend spotting
While doing your routine analysis, it’s essential to focus on two key aspects: patterns and trends in the data. Consider what recurring elements are present in your incidents. These could be related to specific times, locations, or even involve particular employees. Identifying these common factors is crucial because it enables you to take targeted action to address them.
Dedicate time to thoroughly examine your incident records. Conduct an incident analysis that specifically search for these recurring elements. Often, you might uncover surprising patterns that weren’t initially apparent. It’s important to remember that even the most obvious trends can go unnoticed without deliberate and regular examination. By actively looking for these patterns, you gain valuable insights that can guide more effective and informed decision-making.
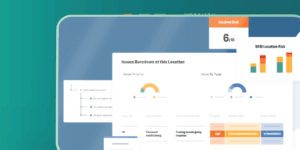
10. Use your results to assess, manage, and mitigate risk
Effective threat assessment hinges on the availability of historical data or empirical evidence. This data is crucial in understanding the nature, frequency, location, and cost of potential threats. By meticulously documenting incidents, you establish a base for decision-making grounded in knowledge, thus empowering you with the necessary tools to identify patterns and assess performance. Ultimately, it enables you to implement strategies for risk mitigation and more effectively developing a robust risk management framework.
Simplify your incident analysis with Resolver
From the nuances of initial documentation to the complexities of root cause analysis, it’s clear that the path to effective incident management is multifaceted. But remember, the journey doesn’t end here. To truly master incident analysis, continuous learning and application of these practices are key.
Interested in taking your incident analysis skills to the next level? Download our comprehensive guide at the top of this page to delve even deeper into these strategies.
If you’re ready to see how cutting-edge technology can transform your approach, why not sign up for a custom demo of Resolver’s Incident Management software? It’s your opportunity to experience firsthand how technology can streamline and enhance your incident response.