It should come as no surprise that a critical aspect impacting the bottom line of many retail establishments is theft. Though many companies put efforts into preventing external theft, cases of internal and employee theft are becoming more prevalent.
While these terms are often used interchangeably, internal theft casts a wide net, encompassing any theft or loss within an organization, regardless of the perpetrator’s affiliation. This can involve a range of individuals including employees, visitors, or contractors. On the other hand, retail employee theft narrows the focus, honing in on instances of dishonest activities carried out by individuals on the company’s payroll.
All employee theft is essentially a form of internal theft, but not all internal theft is necessarily committed by employees. Despite training and implementing policies to deter employee theft, the risk of employee theft is still present. Here are five ways to effectively track and prevent retail employee theft.
Also read: Top 5 Retail Loss Prevention Techniques for 2023
1. Surveillance systems
Strategically installing high-quality cameras at entrances, cash registers, and crucial storage areas is an immediate deterrent, discouraging the potential of retail employee theft. When staff members are aware of being under constant watch, especially in high-traffic areas, it significantly reduces the likelihood of theft.
Fostering awareness among employees about the presence and importance of surveillance reinforces the role of cameras in maintaining a secure and trustworthy retail environment. Additionally, in the event of suspicious activities or incidents, clear and high-resolution footage provides a definitive record that can be used for legal purposes or internal reviews.
Surveillance systems offer real-time monitoring capabilities, enabling management to promptly respond to incidents of theft. Integrating surveillance systems with other security measures, such as access control or alarm systems, enhances the overall effectiveness in preventing retail employee theft. Suspicious activities captured on camera can trigger immediate responses or alerts, creating a seamless and integrated security infrastructure.
2. Point of sale monitoring
Monitoring transactions isn’t just a clerical task in a retail environment. Integrating point of sale (POS) software equipped to detect anomalies like voided transactions and steep discounts is an effective tool to track potential retail employee theft. Regularly reviewing transaction logs should become a routine for management to uncover any irregularities and sound the alarm for a thorough investigation. This can help prevent theft related to gift cards, pre-paid credit cards, and scanning practices which are key factors that contribute to retail employee theft.
Effectively implementing POS monitoring is part of a comprehensive loss prevention and retail employee theft prevention strategy. Include advanced monitoring features within the system that can automatically flag suspicious activities and set up alerts to notify management in real-time when predefined thresholds are crossed. Integrating them with other systems, such as surveillance cameras and inventory management, provides a comprehensive view of potential theft incidents and enables a more holistic approach to loss prevention.
Regularly reviewing transaction logs helps to identify trends, patterns, or specific transactions that may require further investigation. It’s important to clearly communicate to employees that transactions are being monitored for integrity purposes to reinforce the importance of adherence to company policies and ethical conduct. Communicating these policies with employees reinforces the message that unethical behavior will be identified and addressed.
Read more: Business Intelligence Reporting Tools That Security Leaders Need Now
3. Data analytics and pattern recognition
Fusing data analytics and pattern recognition is an effective strategy against retail employee theft. Successfully doing so involves meticulously examining transaction data and employee behavior, unveiling patterns that may signify potential theft. While data analytics detects system disparities like consistent voided transactions or irregular cash handling, behavioral analysis delves into deviations such as unusual working hours or shifts in transaction patterns.
By cross-referencing suspicious patterns identified through data analysis with real-time surveillance footage, retailers gain a comprehensive understanding of potential incidents. This integration ensures a holistic view, leaving no room for blind spots and forming a robust defense against employee theft.
Taking it one step further, creating predictive models can allow you to anticipate potential retail employee theft based on historical data, enabling proactive measures during high-risk periods, in specific locations, or with certain products. Regular updates and refinement of data analytics tools become imperative, ensuring that the system remains adaptive to new patterns and tactics in the ever-shifting landscape of retail security.
4. Inventory control and audits
When it comes to the front lines, inventory control and audits step into the spotlight, offering a proactive means of tracking discrepancies between recorded and actual stock levels. It’s the systematic checking and rechecking and manual and automated processes, supplemented by the precision of barcode and RFID technologies. This ensures that inventory irregularities are swiftly identified and rectified.
Inventory control and audits play a pivotal role in tracking and preventing retail employee theft. Discrepancies, such as missing items or incorrect counts, can be early indicators of potential employee theft. Mitigating this involves continuous tracking and periodic audits to identify trends and patterns in inventory discrepancies. Utilize inventory management software that provides detailed reports on stock movements. Regularly analyzing reports can identify any irregularities or patterns that may require further investigation.
However, it’s important to note that predictable audit schedules may enable employees to attempt to manipulate records. Developing a flexible audit schedule that includes both routine and surprise audits enhances the effectiveness of the audit process.
5. Restrict access
Restricting access is a tactical maneuver that limits entry to sensitive areas and involves limiting entry to sensitive areas based on job responsibilities, thereby reducing opportunities for theft.
By restricting access, retailers can proactively address the principle of crime prevention, controlling entry to potential targets and minimizing the likelihood of internal theft. This is achieved through implementing access control systems that tailor permissions to specific roles, creating internal segmentation within the workplace. Regular reviews of access permissions ensure that outdated rights are promptly updated, maintaining a robust defense against potential vulnerabilities.
Monitoring and logging access activities can create an audit trail that fosters transparency and accountability. Regular reviews of access logs and communicating the importance of following access protocols contribute to a secure work environment.
Track & prevent retail employee theft with Resolver
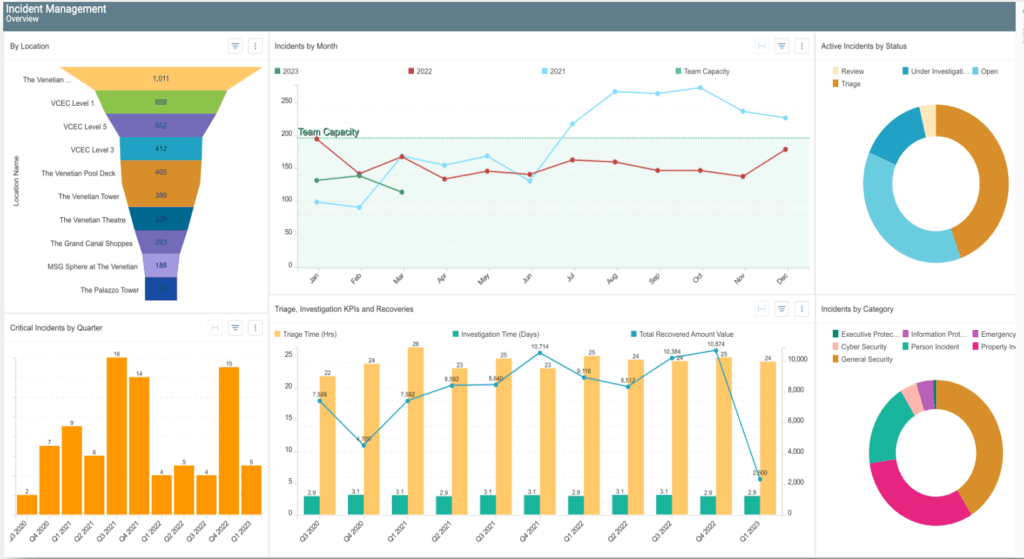
Preventing retail employee theft involves both technological fortifications and fostering a culture where integrity thrives. Employee training, clear policies, and anonymous reporting mechanisms serve as the ethical compass guiding individuals towards the path of honesty, but more can be done. Integrating advanced technologies like Resolver’s Incident Management (IM) system further elevates this defense, offering a comprehensive solution to track, prevent, and respond to incidents of employee theft.
Our IM solution seamlessly integrates into your existing security infrastructure, offering real-time insights, incident tracking, and a proactive approach to loss prevention. Watch a product showcase today to safeguard, empower and elevate the defenses in your business.

