The key to reporting for security teams is to start with good-quality data. There are many tactics that can help you focus on what data will have the most impact in order to provide meaningful insights, but first, you and your team need to clearly define what information you should be actively tracking as part of your security incident management process.
Every business has its own unique incidents, which means that unfortunately, there isn’t a one-size-fits-all approach to apply when it comes to creating a security incident management program. There are several categories that should be considered when developing an incident tracking process.
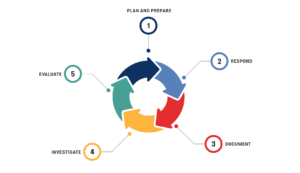
Steps to creating a security incident management program
Creating a security incident management program is essential for any organization to quickly and effectively handle unexpected issues, minimizing disruptions and maintaining operational continuity. The process involves several critical steps so organizations can ensure a swift response to incidents, reducing their impact and preventing small issues from escalating into major problems.
1. Identifying potential incidents
When creating a security incident management program, you should begin with identifying potential incidents that could disrupt your operations. Conducting a comprehensive risk assessment to pinpoint vulnerabilities across various departments and processes is a good place to start. First, compile a list of all possible threats, ranging from cybersecurity breaches and natural disasters to equipment failures and human errors. Engage with team members from different areas to gain diverse perspectives on potential risks. Utilize historical data and industry reports to add to your list.
Next, categorize these incidents based on their likelihood and potential impact. High-risk, high-impact security incidents should be prioritized. Implement tools and systems to help detect early signs of these incidents. For example, network monitoring software can alert you to unusual activity that might indicate a security breach, while regular equipment inspections can preempt mechanical failures.
2. Establishing a clear response plan
Once potential incidents are identified, the next step in creating a security incident management program is establishing a clear response plan. Outline the specific actions to take when an incident occurs, aiming to minimize its impact and promptly restore normal operations. Define roles and responsibilities for your incident response team, ensuring that each member knows their specific tasks, from initial detection and reporting to executing recovery procedures.
Develop detailed protocols for different types of security incidents that include step-by-step instructions for containment, eradication, and recovery. For example, in the case of a cybersecurity breach, your plan might include immediate steps to isolate affected systems, identify the breach source, and restore compromised data from backups.
Communication is critical during an incident. Establish clear communication channels and protocols to ensure timely and accurate information flow among team members and stakeholders. Regularly review and test your response plan through drills and simulations to identify any weaknesses and ensure everyone is familiar with their roles.

3. Training staff
Your team needs to be well-prepared to efficiently and effectively handle security incidents. Begin by providing comprehensive training that covers the basics of incident management, including recognizing early warning signs, reporting procedures, and response protocols.
Tailor the training to different roles within your organization. Use a mix of methods, including workshops, e-learning modules, and hands-on simulations to ensure engagement and retention of information.
Moreover, make security incident management training an integral part of the onboarding process for new employees. By doing so, you ensure that everyone in the organization is equipped with the knowledge and skills necessary to contribute to effective incident management from day one.
4. Continuously monitoring and improving the program
The final step in creating a security incident management program is regularly assessing and refining your incident management processes to ensure they remain effective and responsive to new threats.
Establish key performance indicators (KPIs) to measure the effectiveness of your security incident management efforts. Common KPIs include response time, resolution time, and the number of incidents resolved within a specific timeframe. Regularly review these metrics to identify areas for improvement.
Implement a feedback loop that includes post-incident reviews. After each incident, conduct a thorough analysis to understand what worked well and what didn’t. Gather insights from all involved parties and document lessons learned. Use this information to update your response plan and training programs.
Stay informed about emerging threats and best practices in incident management. Participate in industry forums, subscribe to relevant publications, and invest in ongoing education for your incident response team.
Trends to track in incident reports
When creating a security incident management program, it’s crucial to track key metrics and trends to continuously improve the program and ensure it aligns with business goals and critical success factors.
- Incident category: Different data is required to be tracked for different incident types. For instance, what you track for a slip and fall will be quite different from what you track for internal fraud. That way, you can better determine the associated workflow that gets triggered.
- Severity: A critical element of resource allocation is to measure the severity of each incident. Resources should be allocated primarily to manage and reduce more severe incidents.
- Incident owner: Who is the person (s) assigned to manage the incident and ensure that it moves through the appropriate stages to be closed?
- Date and time: This can be as simple as a single date of when the incident happened, or as complex as tracking the start and end date if an investigation or case is opened as a result of the incident.
- Incident status: Where is the incident in the workflow process? This will vary depending on how complex your organization’s workflow is, but the labels could be simplified to better streamline your process.
- Description: What happened? Where did the incident occur? Who reported it? Who was involved? What are the next steps? Include as many details as possible. It’s best to do so soon after the investigation so specific occurrences aren’t missed.
Improving the quality of your incident data
Now that you’ve documented the basic information for creating a security incident management program, there are additional things you can track to improve the quality of your data. Ultimately, this will allow you to draw more meaningful insights from your reporting.
Who reported the incident?
At a minimum, capturing where and if possible, who submitted the incident should be required. This helps your team identify the correct contact person if more information is necessary to proceed. If submissions are processed through an incident submission portal, it’s helpful to collect more specific information. This can include details about the location and the person reporting the incident. By doing so, you can accurately report on the volume of incidents received per channel.
Location, location, location
Of course, it’s critical to know where the incident took place. This could simply be the address, depending on how your organization is structured. Or, it could go further and track specific departmental locations within your office, or even areas outside in which incidents may occur.
Who’s involved?
Involvement is tracking entities linked to the incident. These include:
- Involved people (suspect, victim, witness)
- Involved organizations (vendor, customer, law enforcement)
- Involved items (laptop, machine, server)
In simple cases, use a single field for tracking when creating a security incident management program. For more complex cases, track attributes of these entities. Linking people, items, and organizations in a system enhances the ability to find connections between incidents.
Losses and recoveries
Tracking losses is a critical component when building a business case for additional security resources. It can be as simple as putting a single value on the incident or as complicated as tracking a list of losses and recoveries tied to specific assets or items.
Defining narratives
Narratives are used for witness or suspect statements. When submitted as evidence, additional steps are necessary. Security teams could build a workflow when creating a security incident management program that locks the narrative from changes. Alternatively, you can maintain an audit trail for verification.
Include additional fields
Depending on your organization and the severity of incidents, there may be a need to track additional incident information. Including fields such as business unit, incident flags, and additional responses enhances the quality of incident data. It provides a more comprehensive view of each incident, which is a key consideration when creating a security incident management program. With detailed tracking, you can pinpoint trends, improve response strategies, and ensure compliance with legal and organizational requirements. It also facilitates better coordination among departments and external agencies involved in incident resolution.
Additional incident information to track for mature security teams
For more mature security teams, there is additional information that can be linked together to provide additional insight. These teams may want to consider the following when creating a security incident management program:
- Related incidents: It’s helpful to link together incidents that are related (i.e. multiple incidents that involve a specific criminal organization.)
- Cases: If one or more incidents escalate to a case, accessing relevant information it’s critical to understand where investigators need to be assigned to do more analysis or collect any additional evidence.
- Tasks and action plans: For more complex incidents, the ability to assign tasks or create action plans linked to an incident can help to reduce the time to close the incident.
- Risks: For organizations that have implemented Security Risk Management software, it’s helpful to link an incident to a specific risk. This along with links to the business unit or location help the security department engage the wider organization to deploy resources and reduce overall risk.
- Root cause analysis: More mature teams will go a step further on complex incidents and perform a root cause analysis. These causes can be attached to the specific incident for future trending.
How to keep security incident reporting simple
Effective security incident reporting is generally a tradeoff between ease of use and depth of data submitted. If you’re still in the early stages of creating your incident management program, start your incident tracking as simply as possible. The more information required from users, the more likely it is that mistakes will be made. Start with the information you need reporting and the data required to adequately address incidents. If you find gaps, add more steps.
Creating a security incident management program is essential for any organization aiming to enhance security and minimize risks. Resolver’s Security Risk Management software helps to reduce the frequency and severity of incidents by analyzing risk data, allowing you to prioritize actions and investments effectively.
With Resolver, you can identify and log critical assets, risks, and controls at each location. Our solution provides security teams with pre-built forms for accurate risk assessments. It also captures and integrates risk, incident, and threat data in a central database, offering a comprehensive risk picture.
Enhance your incident management program with Resolver’s Security Risk Management software. Request a demo today to see our solutions in action!
