Malicious coordinated network exploits Ukraine war to amplify malware on mainstream platform

Overview
Malicious actors operating on mainstream social media platforms are employing deceptive tactics to capitalize on the news cycle around major geopolitical events to disseminate malicious links. These tactics include the use of misleading thumbnail images, targeted hashtags, evocative language and URL shorteners to ensnare and infect their browsers with Infostealer malware.
This investigation decodes the methodology employed by one coordinated network to amplify malware on a mainstream platform and the cost-effective techniques used to masquerade the malicious URLs as traditional media coverage and graphic combat of the Russia-Ukraine conflict. At the time of analysis, the network was able to accrue over 9 million impressions on the platform, including being amplified by accounts belonging to senior politicians in Mongolia and Poland.
A review of the on-platform activity of the malicious network underlines how the proliferation of negative, spam and malicious content, particularly content impersonating credible sources such as media outlets, brand owned-pages and online communities, pose a serious risk to user safety, brand and platform reputation online.
The drive-by download attack
Click bait is an effective tactic that can be enhanced via platform features such as hashtags, as well as through content feeds often represented within the ‘explore’ or ‘you may like’ pages.
After clicking the link, users may be directly infected, or redirected to websites which themselves contain links to malware downloads. This method has been coined as a ‘drive-by download attack’. These types of attacks are most effective when used in conjunction with popular and current news topics. Previous examples include the FIFA World Cup and the Super Bowl. As a prominent geopolitical event with substantial media coverage, the ongoing conflict in Ukraine provides ample opportunity for attackers to create emotive content which may entice users into clicking on malicious links.
A popular form of ‘drive-by download’ attacks involves the deployment of “info stealer” malware, programs that steal sensitive data from infected browsers. This data can include authentication data, usernames, passwords, session cookies, and even personal identifiable information (PII) such as credit card numbers, banking details, and data relating to crypto wallets. Moreover, in December 2023, Techopedia projected the use of infostealer malware by cybercriminals as one of the top 10 cybersecurity trends for 2024, warning that such actors can ‘leverage this data in various ways, and many sell it on the darknet for financial gain’.
Evaluating spread of the malicious URL
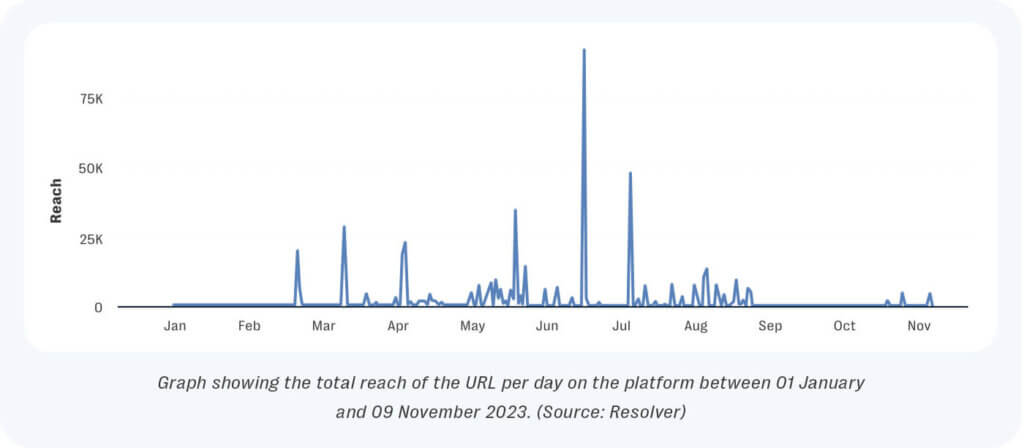
A review of popular posts revealed an abundance of content amplifying images and media alongside a suspicious URL link: ‘twtubekb9[.]page[.]link’. We employed open-source analysis to review all mentions of the URL across popular social networking platforms between January 1, 2023 and November 9, 2023. This examination showed the link was exclusively amplified on a single platform where it received 100,872 mentions from just 261 unique authors over the examined time period.

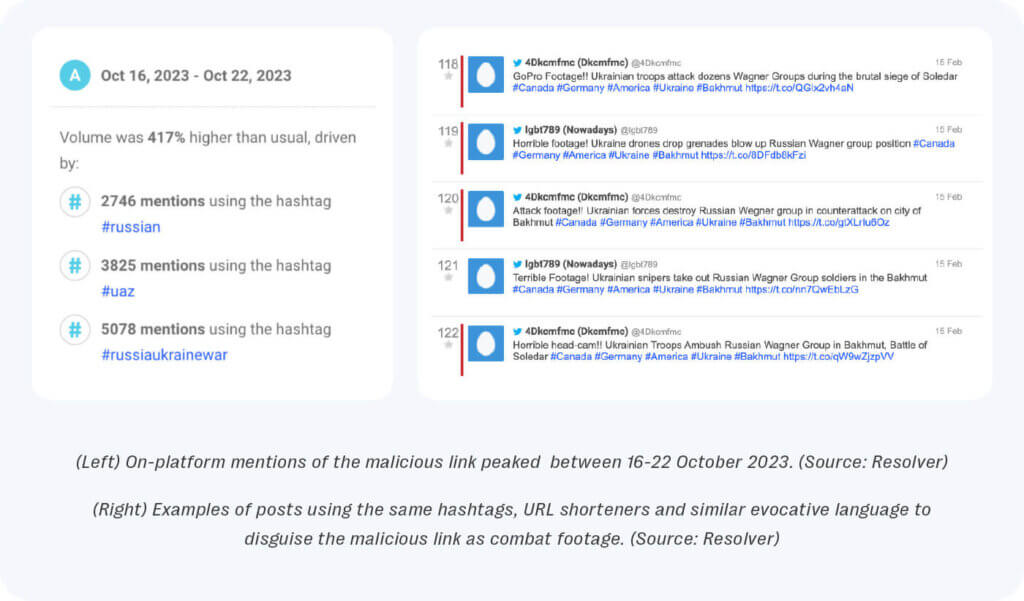
Closer scrutiny of the mention volume over time on the platform, revealed that it was first amplified on February 13, 2023 with 122 mentions, while on-platform activity for the URL peaked on October 16, 2023 with 10,338 mentions. Between October 16 – 22, mentions of the URL spiked by 417% on the platform, with this engagement driven by thousands of near identical posts that attempted to disguise the URL as combat footage depicting heavy losses suffered by Wagner private military company soldiers at the hands of Ukrainian troops in Bakhmut. The URL purported to direct users towards a video-hosting platform that was inactive at the time of analysis.
However, the team was able to discover a different website that followed the same naming convention, k9b[.]tube2[.]m. Like the former URL, this secondary link was also shared across the same platform, by accounts which exhibited several characteristics associated with inauthentic activity. Additionally, the website contained videos with descriptions and titles that shared common naming conventions as the former inactive website.
Further scrutiny of this second website’s outbound traffic revealed that 18% of users accessing the website were redirected to a third-party malicious service which tricks the user into granting permissions via their browser for the site to send spam ads and notifications directly to their device. Meanwhile, sandbox analysis of the two websites also revealed they both dropped a common file, “Part-RU”. This file was flagged by the sandboxing software as being “malicious”.
Closer examination via open source threat intelligence platforms of the “Part-RU” file associated with both websites, revealed that the file belongs to the RedLine Stealer malware family. This software is sold at relatively low cost on dark web marketplaces. This type of malware is reported to steal information directly from infected user’s browsers, including login details, autocomplete, passwords, and credit cards. It also collects information about the user and their system such as the username, hardware configuration, and installed security software.
The command-and-control server listed for the malware sample was also tracked by Kroll Cyber Threat Intelligence (CTI) who had also categorized it as a Redline stealer in their database since January 2022. The team also observed other instances of threat actors leveraging the video-descriptions under posts on a mainstream video-sharing platform to amplify Infostealer malware providing further evidence of how mainstream social platforms form an intrinsic part of the distribution strategy used by threat actors to ensnare new victims.
The compromise of browser credentials of employees may have adverse financial and reputational impacts on individuals and organizations as this personal data can be sold or reused to facilitate future cyber attacks.
Anatomy of a deceptive malware campaign
#1 Top amplifiers exhibit signs of inauthenticity
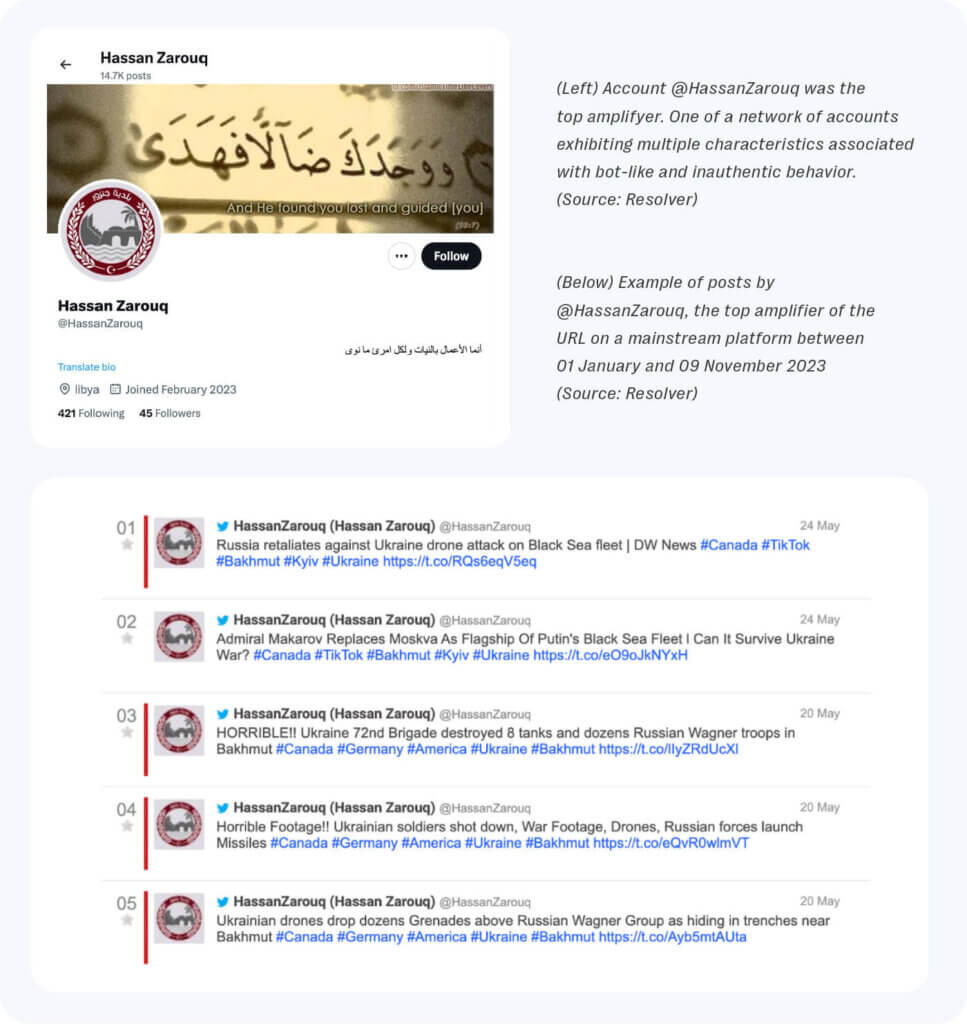
Further investigation of the top ten amplifiers by volume of the malicious URL on the platform revealed the URL was spammed tens of thousands of times by individual accounts with small followings that exhibited several characteristics associated with inauthenticity. These characteristics include maintaining functional anonymity with no original profile pictures or identifying information, similar account creation dates, and timelines devoted primarily to the amplification of the suspicious link with little to no novel messaging. In particular, just the top ten amplifiers within the broader network accounted for over 81,000 mentions of the URL on the platform over the examined time frame.
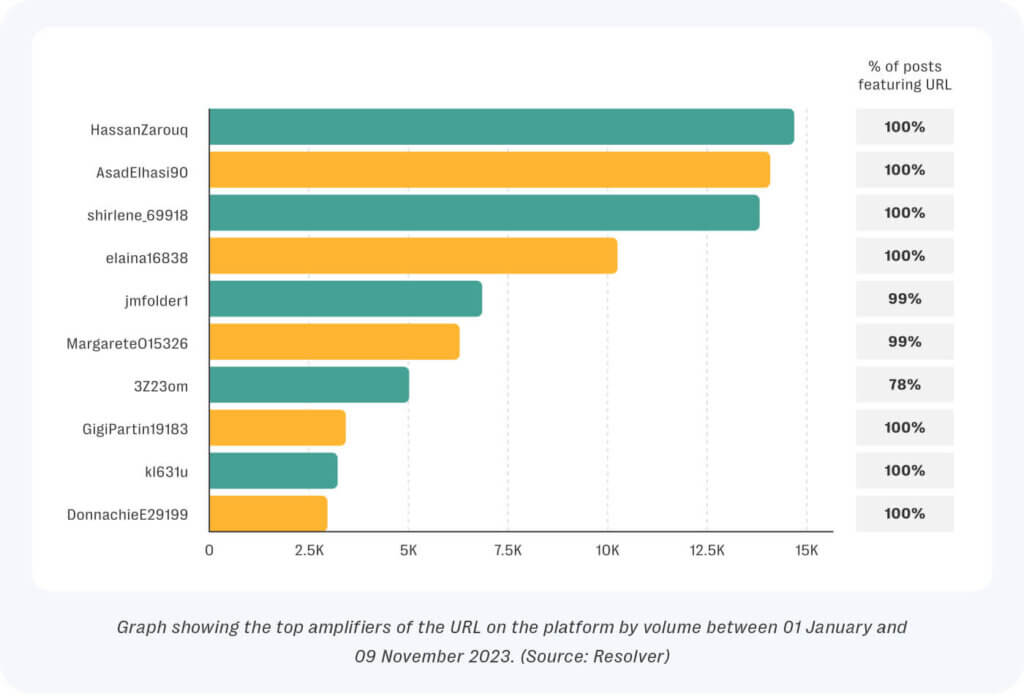
An example of this can be seen when looking at an account on the platform presenting itself as an individual based in Libya. The account maintains functional anonymity and posted the malicious URL 14,645 times between January 1 and November 9, 2023. Further investigation of the account revealed that 99.9% of all account activity consisted solely of amplifying the malicious URL on the platform, with no original content. Over the course of the investigation, several of the top amplifiers of the URL by volume were suspended by the platform.
#2 Provocative language
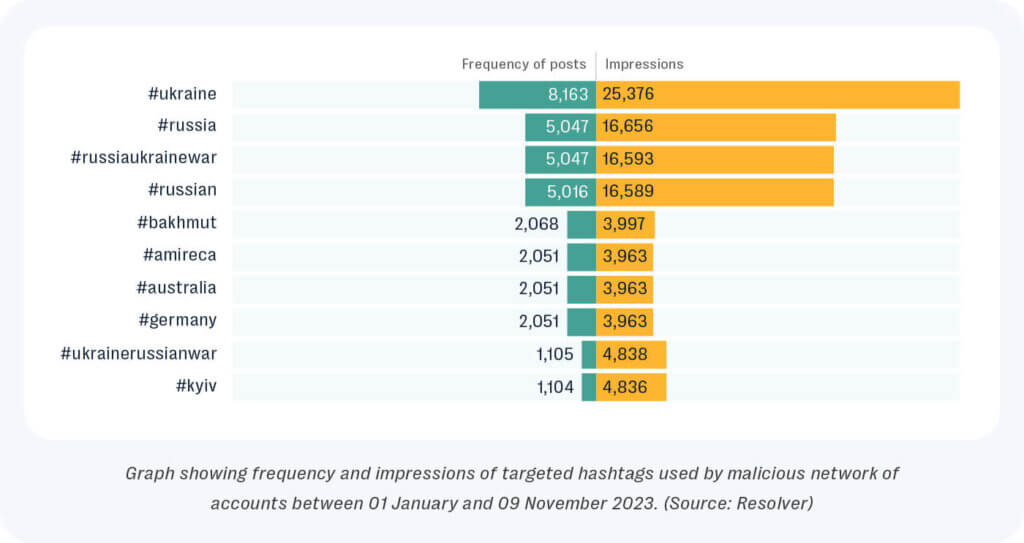
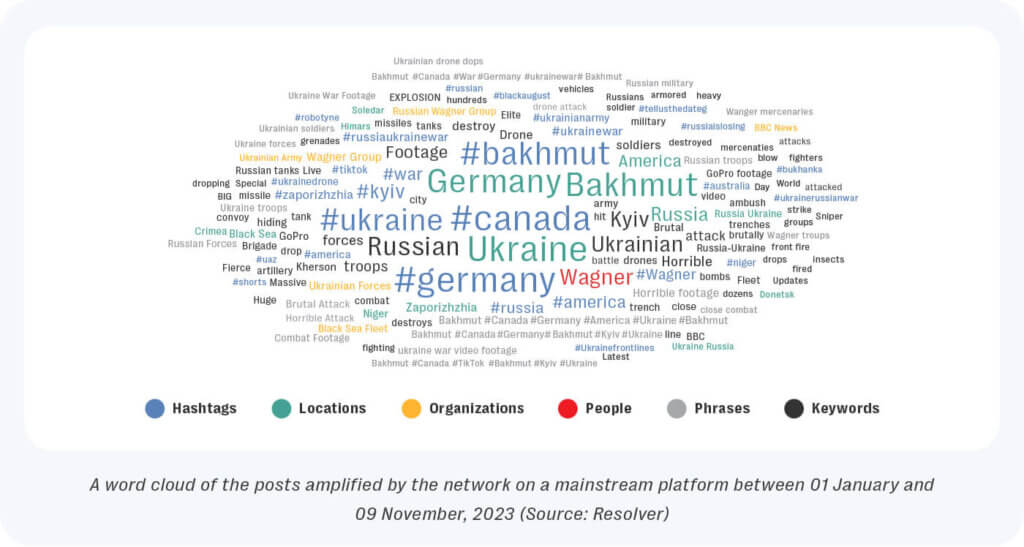
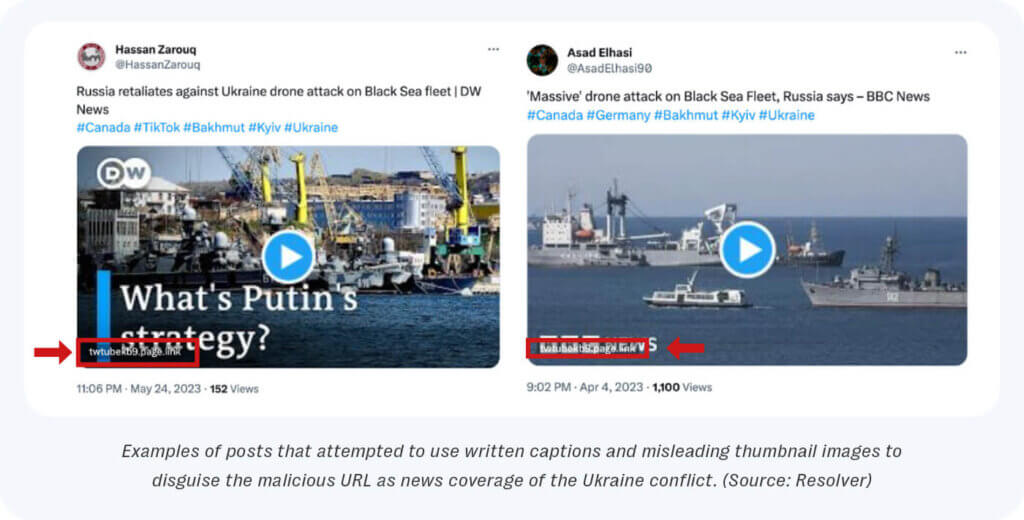
Posts amplifying the URL employed provocative language suggesting the attached media depicted heavy casualties suffered by Russian forces, likely as a means of attracting attention from pro-Ukrainian users. The network also employed targeted hashtags such as #ukraine, #germany, #australia and #amireca [sic] likely as a form of trending topic/hashtag spam to further boost engagement on the URL across the platform.
#3 Misleading thumbnails
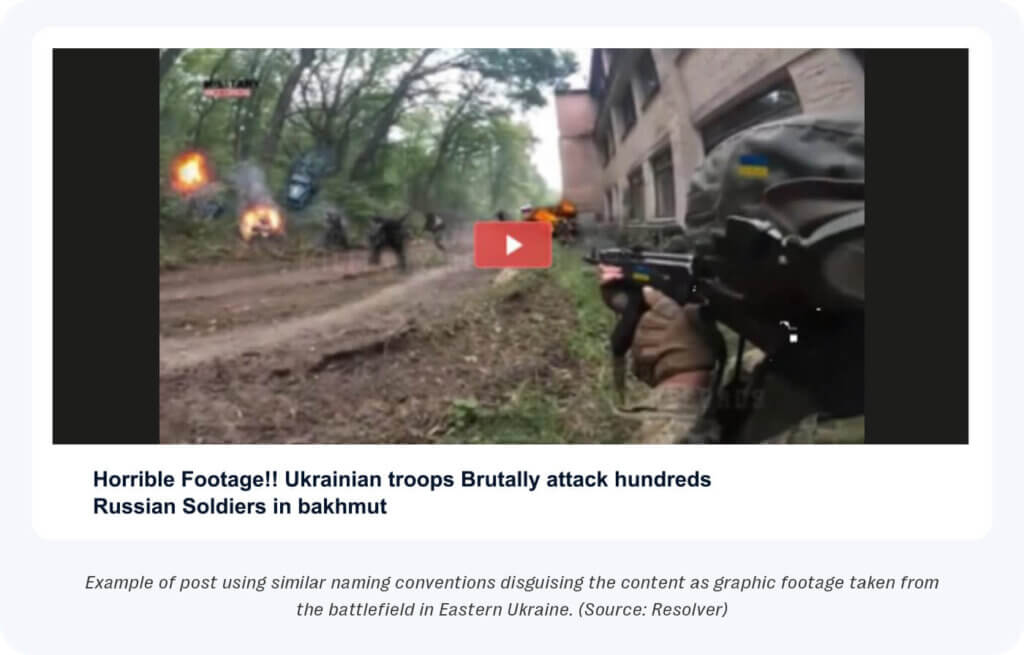
The malicious network amplified the URL alongside provocative written captions, targeted hashtags, and misleading thumbnail images including manipulated stills taken from media reportage of the conflict and other images likely sourced from different first-person-shooter video games to disguise the nature of the malicious link.
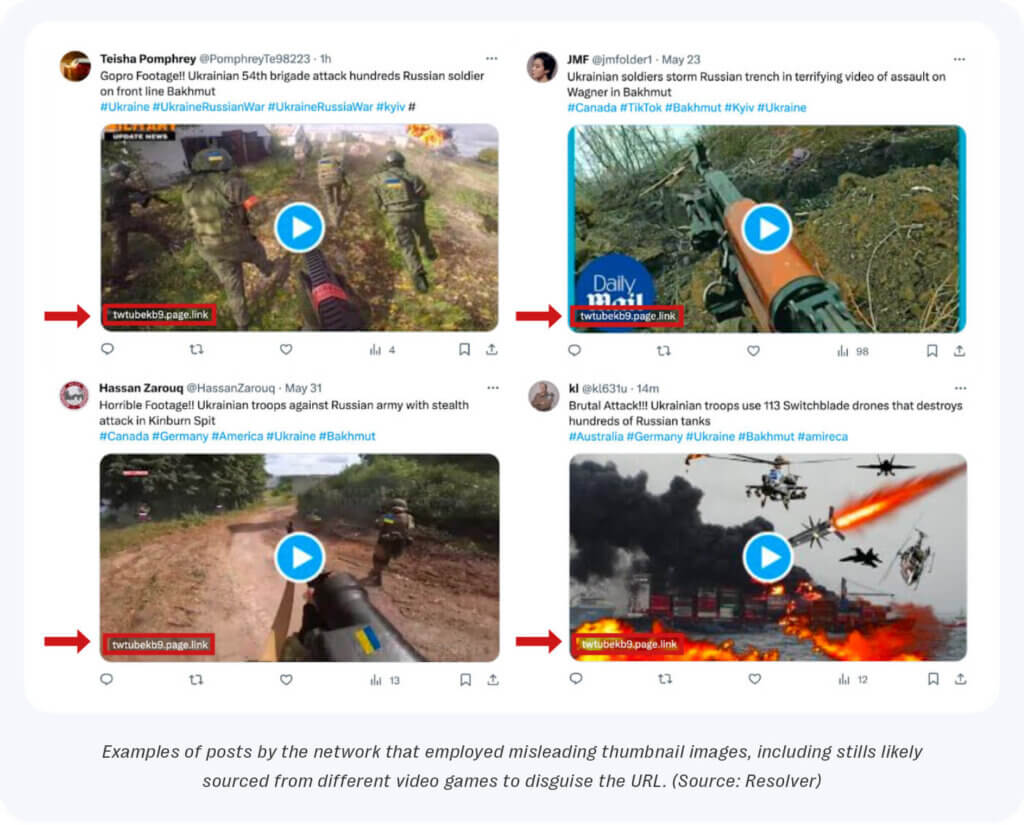
In particular, the use of thumbnail images taken from media videos of the conflict by Western media outlets, such as the BBC, CNN, The Telegraph, and DW, highlights the ease with which bad actors can employ simple cost-effective deceptive techniques to boost the credibility of false and inflammatory narratives. This also aids in amplifying disguised malware across mainstream social media platforms.
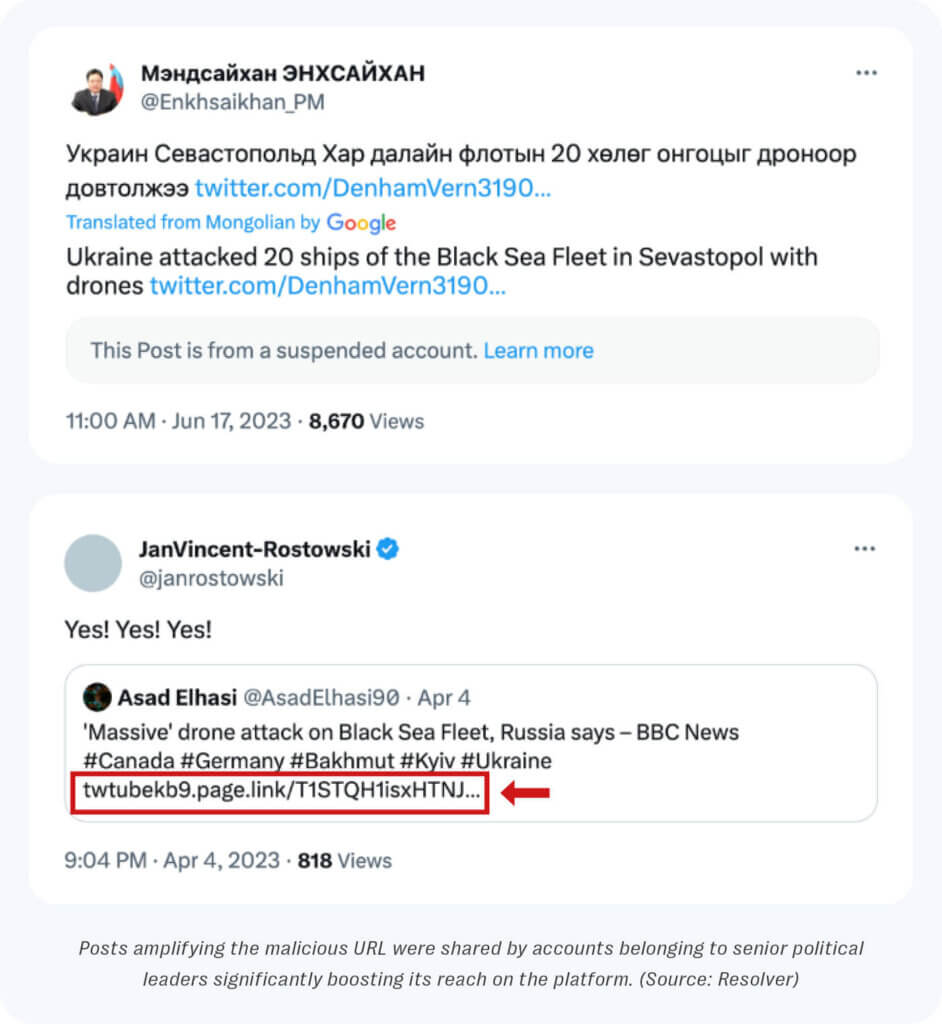
Malware inadvertently amplified by senior politicians
A review of the total impressions gained by the network between January 1, and November 9, 2023 revealed posts amplifying the malicious URL had accrued over 9.6 million impressions (968738) on the platform over the examined time frame. The on-platform reach of the URL peaked on June 17, 2023 with 91,895 impressions. This spike in activity was driven by several accounts with larger followings that shared the posts amplifying the malicious URL to their audience of users on the platform.
These accounts include @Enkhsaikhan_PM and @janrostowski belonging to Mendsaikhany Enkhsaikhan, the former Prime Minister of Mongolia, and Jacek Rostowsky, the former Deputy Prime Minister and Finance Minister of Poland, respectively.
Conclusion
An appraisal of this network of accounts highlights the deceptive tactics employed by malicious actors to disguise the true nature of malware targeted at users on mainstream social media platforms. In particular, the use of provocative language, URL shorteners, targeted hashtags and misleading thumbnails underlines the risks to user and brand safety posed by spam, mis-and disinformation and malware, flooding online communities and disrupting the users platform experience.
For brands and major platforms, Platform Risk Intelligence offers an ideal risk management solution to mitigate against the harms posed by the proliferation of such harmful content across brand owned and managed digital communities. Our solution is capable of quickly identifying and alerting for ‘needle in the haystack’ issues so our partners can proactively act against current and emerging threats and safeguard community and user safety on their platforms.