Top Risks for IT Risk Teams in SaaS Companies

You’d be hard-pressed to find a company that doesn’t rely on technology to run its day-to-day operations. On average, companies have more than 200 apps in their enterprise information technology systems. And companies operating in the SaaS space probably hold many, many more. That’s why SaaS companies fall into a high-risk category. Let’s take a look at some of the top risks for IT teams in SaaS companies.
Data Security and Compliance
High-level compliance management can do more than keep you out of trouble with a regulatory agency. You can leverage compliance as an asset and a business driver to enter a market. Using compliance as a business strategy lets you position your company as a quality alternative in your market space.
To embed compliance into your overall business development, however, requires going beyond minimal obligations for data security and reporting. You have to show potential customers how transparent compliance systems help address a market need and thus improve your competitive advantage.
SOC 2
An auditing procedure developed by the American Institute of CPAs (AICPA), SOC 2 helps ensure that service providers manage data securely. This procedure helps protect organizational interests and client privacy, and it reduces a company’s vulnerability to an attack. Cloud-computing providers and SaaS third-party vendors in particular need to stay compliant with SOC 2.
Designed specifically for service providers that store customer data in the cloud, SOC 2 applies to nearly every SaaS company. Consequently, it serves as one of the most common compliance frameworks, often the first one that SaaS companies choose to comply with.
But SOC 2 is a really just minimal requirement for a SaaS provider, simply ensuring that systems operate in a way that helps assure the security, availability, processing integrity, confidentiality, and privacy of customer data. SOC 2 assures organizations that the vendor’s systems have been configured for maximum data privacy and security.
Staying compliant with this SOC 2 helps can help your company establish and follow security policies and procedures that improve security, availability, processing integrity, and confidentiality.
ISO/IEC 27001
An information security standard first published in 2013 by the International Organization for Standardization and the International Electrotechnical Commission, ISO/IEC 27001 provides a consistent and formal framework for managing IT security. The standard covers more than IT, though, and can apply to many data security controls operating within areas such as human resources, physical security, and operational control.
Compliance with ISO/IEC 27001 includes :
- Monitoring, measurement, analysis, and evaluation of the company’s information security management system;
- Monitoring, reviewing, maintaining, and improving a company’s information security management system.
Knowing that your company has been ISO 27001 certified gives organizations and customers greater confidence in your risk-management strategy as they interact with your business.
HIPAA
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) applies to any company doing business in the healthcare sector. HIPAA is largely known for its privacy rules that determine whom healthcare providers may discuss your medical care with. But HIPAA guards more than that. It also establishes laws regarding the security of medical data called electronic protected health information (ePHI). In fact, HIPAA applies to all systems that are used to transmit, receive, store, or alter electronic protected health information. Any system or software that ‘touches’ ePHI must incorporate appropriate security protections to ensure the confidentiality, integrity, and availability of ePHI.
Location of Data and Complying with Data Privacy Laws
The data privacy laws in effect in your area can have a positive or negative impact on your business, and laws vary widely from region to region.
The European Union (EU) and European Economic Area (EEA) countries, for instance, abide by a central data privacy law called the General Data Protection Regulation (GDPR). GDPR prompted other nations such as Chile, Japan, Brazil, South Korea, Argentina, and Kenya to follow suit. The U.S. also has data privacy laws, but they are not federally centralized. Instead, all 50 U.S. states maintain their own unique data privacy laws under federal guidelines established by legislation such as the U.S. Privacy Act of 1974.
Several states have recently enacted new, stricter laws around cybersecurity, data security, and data breach notification. California in particular has set out a comprehensive legal roadmap around data privacy. Let’s look at three of the most significant data privacy and protection laws from around the world:
GDPR
GDPR is a set of rules designed to give EU citizens more control over their personal data. This legislation establishes regulations surrounding how governments, private companies, and other actors can process the personal data of EU citizens or residents. GDPR established some of the most far-reaching and consequential information security laws in the world to date, and its impact remains the subject of study, controversy, and concern.
California Consumer Privacy Act
The California Consumer Privacy Act (CCPA) requires all companies that serve California residents and bring in $25 million or more in annual revenue to take steps to protect consumer privacy. Besides these large enterprises, any company that possesses personal data on at least 50,000 people or that collects more than half of its revenues from the sale of personal data must also comply with CCPA regulations. Companies don’t have to be based in California or have a physical presence there; in fact, they don’t even have to be based in the U.S. to fall under the law. When the CCPA was passed in 2018, it became the strongest data privacy rights legislation in the country.
CASL
Canada’s Anti-Spam Law (CASL) is one of the world’s toughest but most confusing anti-spam laws. CASL applies to all electronic messages that organizations send in connection to a commercial activity delivered to Canadians and applies to all messages delivered to all Canadians regardless of the location of the business sending the message. Under CASL, all messages that are commercial in nature must have obtained consent and a functioning unsubscribe mechanism in order to be delivered.
Discover Resolver's solutions.
Operations and Loss Control
Smart devices and human beings are the weakest links in any cybersecurity chain. Humans are especially vulnerable when they aren’t regularly connected to the IT security team.
Admin Controls
Organizational administrators maintain contracts, internal procedures, and documenting processes. These documents could hold value to cybercriminals or even to disgruntled employees. IT teams need to ask:
- Who is the on-call team?
- Do they have documented procedures to ensure that they are always up and running?
- Has the administrative team created documentation about applications or a playbook of step-by-step directions for resolution, disaster recovery plans, and business continuity planning?
Technical Controls
Keeping downtime to a minimum is a critical function for IT security teams. The current industry standard is an uptime of 99.99%. Here are three strategies for maintaining or improving uptime:
- Alerting: Put in place systems that notify the on-call team of any potential issues.
- Centralized logging: Collect logs of everything that transpires to a) document everything that takes place and b) establish the root causes. By documenting the timeline of the steps taken to resolve the issue, you create a map of countermeasures that technicians can take to avoid problems in the future.
- Redundancy: Design a system that includes redundancies to avoid impacting customers. The service level agreement will dictate how many layers of redundancies you actually need.
Cybersecurity
Cybersecurity is concerned with external threats such as hacking, spyware, ransomware, and malware. Cybersecurity is only one component of a robust organizational security initiative, but it’s often the one that generates the most attention from the C-suite and the corporate board. Many executive leaders need comprehensive education on what cybersecurity is and aren’t and how it can actually be carried out in the workplace.
Security Awareness Program
Since humans are the most vulnerable point of entry for any organization, the best cybersecurity initiative probably isn’t software. It’s internal training. Creating a corporate culture of security awareness is necessary to ensure security in an organization. Training should include topics such as social engineering, phishing, and other attack techniques. By implementing what they learn in training, employees can realize the potential impact of what could happen by simply opening a fishy email or leaving codes unattended on their desks.
Firewalls
Firewalls can prevent unauthorized network traffic from reaching network services. Most experts recommend that you audit and update your firewall rules at least once a quarter. Depending on your business and your cybersecurity threat level, you may want to do it more often than that. Firewall log reviews should also be a part of your alerting and monitoring process.
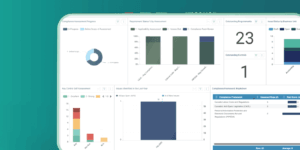
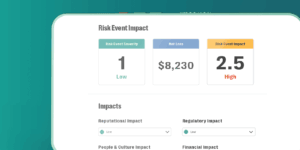
How SaaS Companies Can Mitigate IT Risks
Resolver’s IT Risk and Compliance Management Software automates IT risk and compliance processes to reduce the cost, resources, and effort required to effectively manage cybersecurity programs, provide risk oversight to executives and the board, and achieve IT certifications such as SOC 2, ISO 27001, and others.