Conquering Spam: 5 Steps to Safeguard Your Brand’s Online Presence
What’s the leading factor of your brand’s reputation? Like it or not, it’s your social media presence. And social channels are where spam emerges as your reputation’s most formidable adversary. Indeed, social media is the new Wild West for unwanted spam.
Even under ideal circumstances, authentically connecting with your audiences on social media is a hard-won task. Keeping your feed current and your followers focused can be a daily struggle. Add spam, and suddenly, you’re vulnerable to the possibility of distorted brand messaging, community alienation, and even security risks.
And like your social channels, the spam that invades them is constantly evolving. The tactics that spammers wield do change, and the language they use to serve their spammy ways also changes. However, the dangers that lurk are consistent—and often grow in severity.
Protecting your online presence is no longer an option; it’s a mandatory. Let’s start by understanding the nature of spam and recognizing its various forms. Then, we’ll equip you with the artillery to create your best defense.
Spam poses growing threat on social media
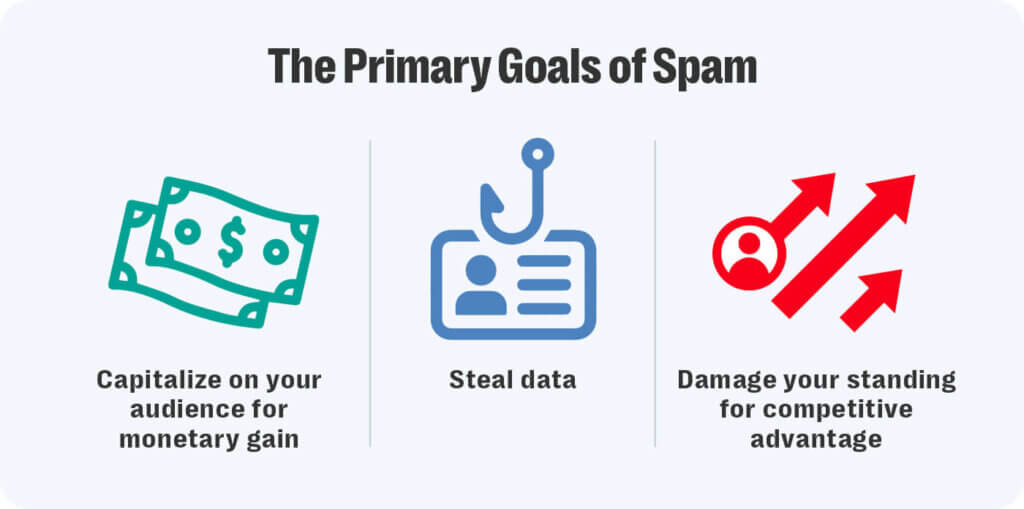
Spam is any unwelcome content that exploits your brand’s digital presence to push irrelevant or malicious content. Examples include those ads you suddenly see on your brand’s social media page for unrelated products, suspicious links that lead down dark-web rabbit holes, and user posts that press your followers to buy their own products.
It’s all designed to leverage your brand’s reach for purposes you would never intend.
Many flavors of spam
Though it seems malicious actors on social media invent new modes of spam nearly every month, here are the most prevalent social spam examples today:
- Commercial advertising. You’re scrolling through your cosmetic company’s Instagram posts about your newest eyeshadow palette, and suddenly, your page is now an ad fest for diet pills. Even though this makes zero promotional sense (you can have smoky eyes without losing weight), it’s unfortunately a classic case of commercial spam.
- Self-promotion. A comment under an athletic shoe brand’s post about a new sneaker drop announces, “Check out my page for more cool kicks!” with an outlink. It’s like inviting yourself to a party when you’re not on the guest list. Self-promo hacks are the freeloaders of social media who turn a brand’s carefully curated post into their personal billboard.
- Suspicious links. A couture-level fashion brand’s Instagram once became a minefield when fake accounts started promoting “exclusive deals” on the brand’s luxury goods—that were actually cheap imitations. Clicking these links led you to a phony site that then took you to a malware-infested knock-off product page. These links are the Internet’s darkest alleyways.
- Inappropriate content. When a family-friendly brand gets comments under their posts pushing everything from risqué adult content to aggressive political propaganda, it’s more than just off-brand—it’s a full-blown crisis. This kind of spam can turn a brand’s social feed from a welcoming community hub into a battleground, concurrently alienating fans and tarnishing the brand’s image.
The phishing threat
A particularly nasty form of spam is phishing, in which spam mimics legitimate brand communications to deceive users into divulging personal information.
For instance, during a highly anticipated sports car launch, followers could encounter fake accounts that mimicked an auto brand’s official social platform, complete with similar usernames and branding. These accounts led followers to counterfeit sites or landing pages that ask for credit card numbers—basically, permission for identity theft.
Challenges in spam detection
Identifying spam involves ethical considerations, particularly regarding user privacy and freedom of expression on your brand’s social channels. You face the constant dilemma of aggressively filtering out spam and risking suppression of legitimate user interactions—or taking a more lenient approach that may allow spam to slip through.
For example, during political elections, a brand has to carefully balance removing genuine political advocacy and filtering out promotional spam without appearing to err on the side of political bias.

Best practices for protection Though there are very few things you can do to prevent spam on your brand’s social channels, you can take these precautionary and corrective measures to ensure spam doesn’t stick around for long:
- Educate your audience. Regularly inform your followers about how to recognize and report spam. This not only helps manage spam but also builds trust with your audience.
- Tighten security settings. Customize your spam filters and privacy settings on each platform to match your brand’s risk level and audience engagement style.
- Monitor consistently. Assign dedicated team members or use a reliable third-party service to actively monitor your social channels. This is vital during high-traffic events or promotional campaigns when spam attacks are likely to spike.
- Engage with transparency. When spam is detected, communicate openly with your audience about what happened and how it’s being handled. This strategy helps maintain trust and, consequently, credibility.
- Implement moderation tools. Complement human intervention with AI-driven tools that can learn and adapt to new spam tactics.
Maintain a cleaner social space
Resolver’s Moderation for Brands solution is a prime example of how to leverage technology to defend against spam. By integrating AI with human intelligence and oversight, we offer a comprehensive solution that keeps user engagement authentic, your online community secure, and your audiences coming back for valuable interaction. Request a demo >






